Kernel security training for your team.
Custom kernel fuzzing and kernel exploitation training, scoped to your team's level and delivered by an active practitioner.
4x DEF CON CTF Finals champion (PPP, 2022-2025) · author of the CMU thesis on Linux kernel fuzzing · syzkaller contributor · former CMU TA and guest instructor for US Army units.
Kernel exploitation and the skills that feed it.
Every engagement is centered on kernel pwn. Fuzzing, triage, and related disciplines are covered as part of the exploit pipeline, scoped to what your team actually needs.
Outcomes depend on the track, but every team leaves a sharper kernel hacker: comfortable standing up a vulnerable kernel, driving bugs to flag or root, and working the tooling around it.
Kernel Exploitation
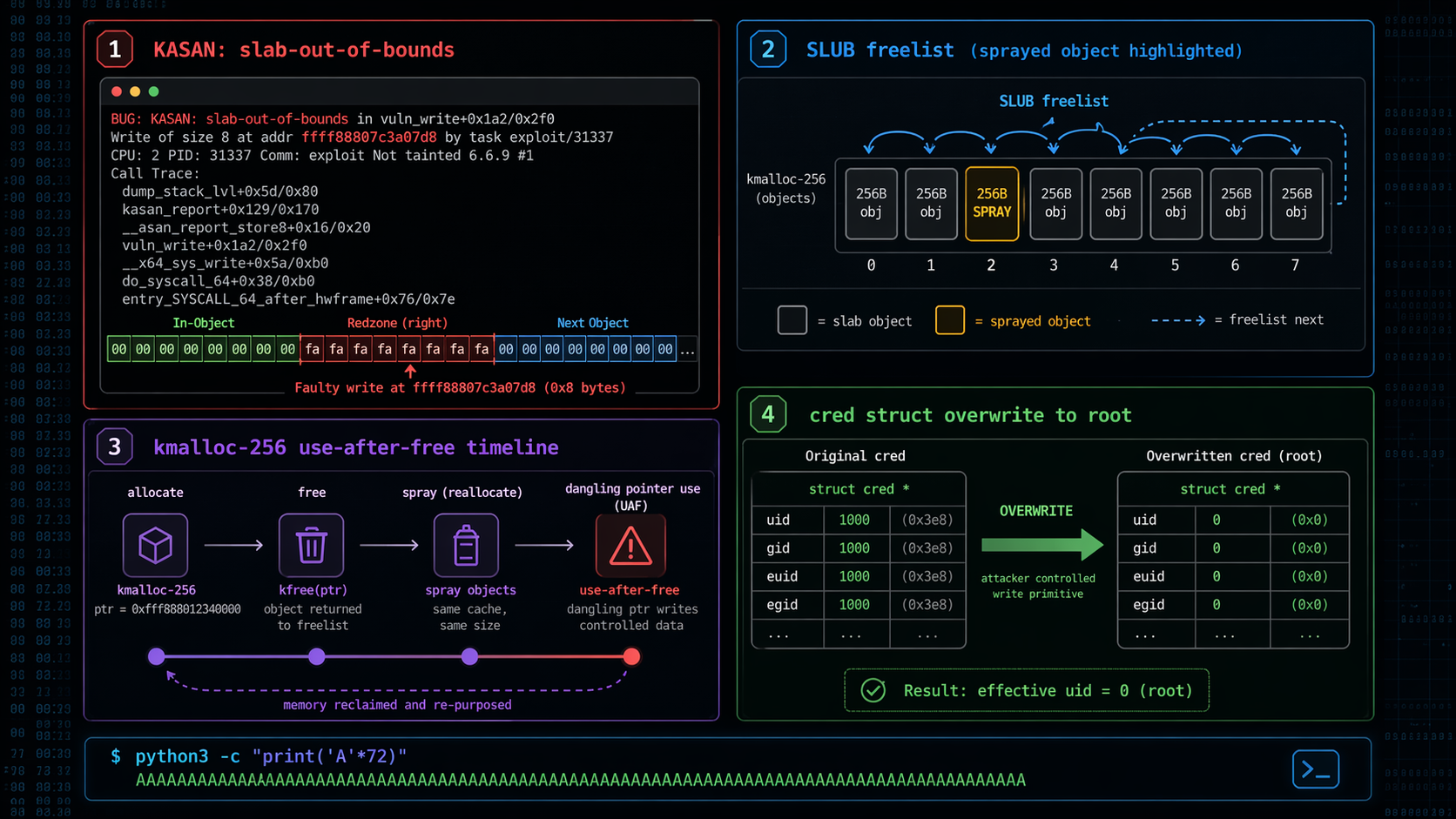
The core of every engagement. Your team learns to turn kernel bug classes into controlled privilege-escalation chains, from trigger reliability and allocator manipulation to mitigation-aware stabilization. Trainees get access to custom kernel pwn tooling built for these labs, so they spend their time on the exploit, not the plumbing.
- Race-condition trigger design and reliability
- SLUB internals and object lifecycle control
- Credential and namespace abuse pathways
- Mitigation-aware exploit stabilization
- End-to-end chain construction and post-exploit analysis
- Custom kernel pwn tooling provided to trainees
Kernel Fuzzing
Finding the bugs that feed the exploit pipeline. Covers syzkaller setup, corpus tuning, crash triage, reproducer minimization, and root-cause analysis so your team can generate its own targets.
- Syzkaller architecture, corpus strategy, and descriptions
- Crash triage with KASAN and KMSAN reports
- Reproducer minimization and flake reduction
- Root-cause analysis workflows
- Connecting fuzzer output to exploitable primitives
- Workflow tips from an active syzkaller contributor
Why train with us.
Active coach, active hacker
Still competing in pwn and kernel CTFs, still fuzzing kernels, still shipping exploits. The material is what I'm working on right now, not notes from a job I left five years ago.
Scoped to your team
Your engineers are met where they are. Background check, skill calibration, and then a syllabus built around the gaps that matter. No one-size-fits-all track.
Hands on the keyboard
Real exploits written, real crashes triaged, real fuzzers stood up. Lectures exist to unblock the lab, not the other way around.
Palash Oswal
Kernel security researcher and practitioner specializing in Linux kernel fuzzing, binary exploitation, and offensive security training.
The questions buyers actually ask.
How is this different from SANS, Offensive Security, or a conference training?
Those are fixed-syllabus courses built for a broad audience. Kernel Pwn engagements are scoped to your team after a short calibration call: we look at who's in the room, what codebase they work on, and what outcome matters, then build the track around that. You're hiring a practitioner who still does the work, not a curriculum.
What kernel do you train on?
Default is upstream Linux on a recent LTS. If your team works against a vendor fork, a downstream Android kernel, or a custom kernel, we can run the labs against that under NDA. I'll tell you up front if something is out of scope for what I can credibly teach.
Is this offensive or defensive training?
Offensive in method, defensive in outcome. Teams leave able to read a crash, drive a bug to exploitation, and reason about what mitigations would have stopped them. That skill set lands the same whether your team is building products, red-teaming, or writing kernel code.
What do my engineers need to know coming in?
Comfortable C, comfortable on a Linux command line, and comfortable reading disassembly or willing to learn fast. Prior userland pwn experience is a plus but not required. During scoping we ask for a rough skill read so we can pitch the labs correctly.
How long are engagements?
Typically three to five days of delivery, depending on depth and how many tracks you want to cover. Shorter bootcamps and longer multi-week engagements are both possible. We scope this after the calibration call.
Remote or on-site?
Remote is the default right now and works well with recorded walkthroughs plus live labs. In-person delivery is available when we're already co-located at a conference. Dedicated on-site travel may be possible for the right engagement, just ask.
Do trainees get tooling to keep after the engagement?
Trainees get access to a set of custom kernel pwn tools built specifically to make these systems easy to work with: dropping into a vulnerable kernel, iterating on exploits, and wiring up fuzzing rigs without fighting the environment. The idea is to keep the labs focused on the hard part, not on scaffolding.
Can you work under NDA against our internal code?
Yes. Mutual NDAs are standard. If your engagement needs a custom lab built against a private kernel tree or internal driver, we'll scope the prep work separately.
How do we start?
Send an inquiry through the form below or email support@hackers.school. We'll follow up with a short calibration call to understand your team, the goal, and the constraints. A scoped proposal follows within a few days.
Let's scope your training.
Tell us about your team and what you're looking for. We'll follow up to discuss scope, format, and scheduling.
Prefer email? Reach us at support@hackers.school.